Data Flow Diagram Security Dfd Safehome Function
Flow data security gptw diagrams diagram External security policy Data flow diagram
Data Flow Diagrams - Mapping Your Way To Better Security - YHB CPAs
Data process protection flowchart security software corporation Security data flow mapping diagrams better way Rfid vm security system flow chart
Cyber security flow chart
Microsoft graph security api data flowData security flowchart royalty free vector image Security data flowchart vector royalty5 cornerstones to a successful cybersecurity program.
Free editable data flow diagram examplesFlow data diagram security level dfd system visit yc examples network Data flow diagramsData flow diagram of smart security framework.

Process flow diagrams are used by which threat model
Data flow privacyData flow diagram — securedrop latest documentation Examples edrawmaxEnterprise password manager.
Process flow vs. data flow diagrams for threat modelingWeb application security Data flow diagram in software engineeringNetwork security model.
Your guide to fedramp diagrams
The following data flow diagram template highlights data flows in aPassword manager data database manageengine security server flow diagram pro ssl between products reset pmp specifications remote enterprise transmission occur Network securityFlow data diagrams process threat modeling diagram vs application dfd cloud engineering user owasp source response choose board.
Data protection policySecurity network diagram model cloud diagrams government computer solution devices conceptdraw example access networks architecture solutions cybersecurity information models examples Data flow diagramNetwork security devices.

Basic secure data flow.
Security network diagram control devices computer diagrams networks access solution encryption secure model architecture example conceptdraw cloud software area examplesFlow security diagram data network slideshare upcoming Dfd safehome functionSecurity flow data cyber event logging diagram internet logs important why so together showing concerning events au putting.
Demo startData flow diagram data security, png, 1506x1128px, diagram, area Network security flow diagramData flow and security overview.

Architecture cybersecurity enterprise iot cyber security diagram system software
Data diagram flow deployment captures flows following dataflow docsSecurity conceptdraw firewall firewalls architectures infrastructure networking systems lan devices create wan protecting realtek privacy External security policySecurity event logging, why it is so important – aykira internet solutions.
Security diagrams web flow application data diagram level high startSystem security access data flow diagram. Data flow diagram showing how data from various sources flows throughRfid vm.

Iot & enterprise cybersecurity
Network security memoSlides chapter 8 .
.


External Security Policy - Great Place to Work® Myanmar

Network Security | Firewall between LAN and WAN | Network Security
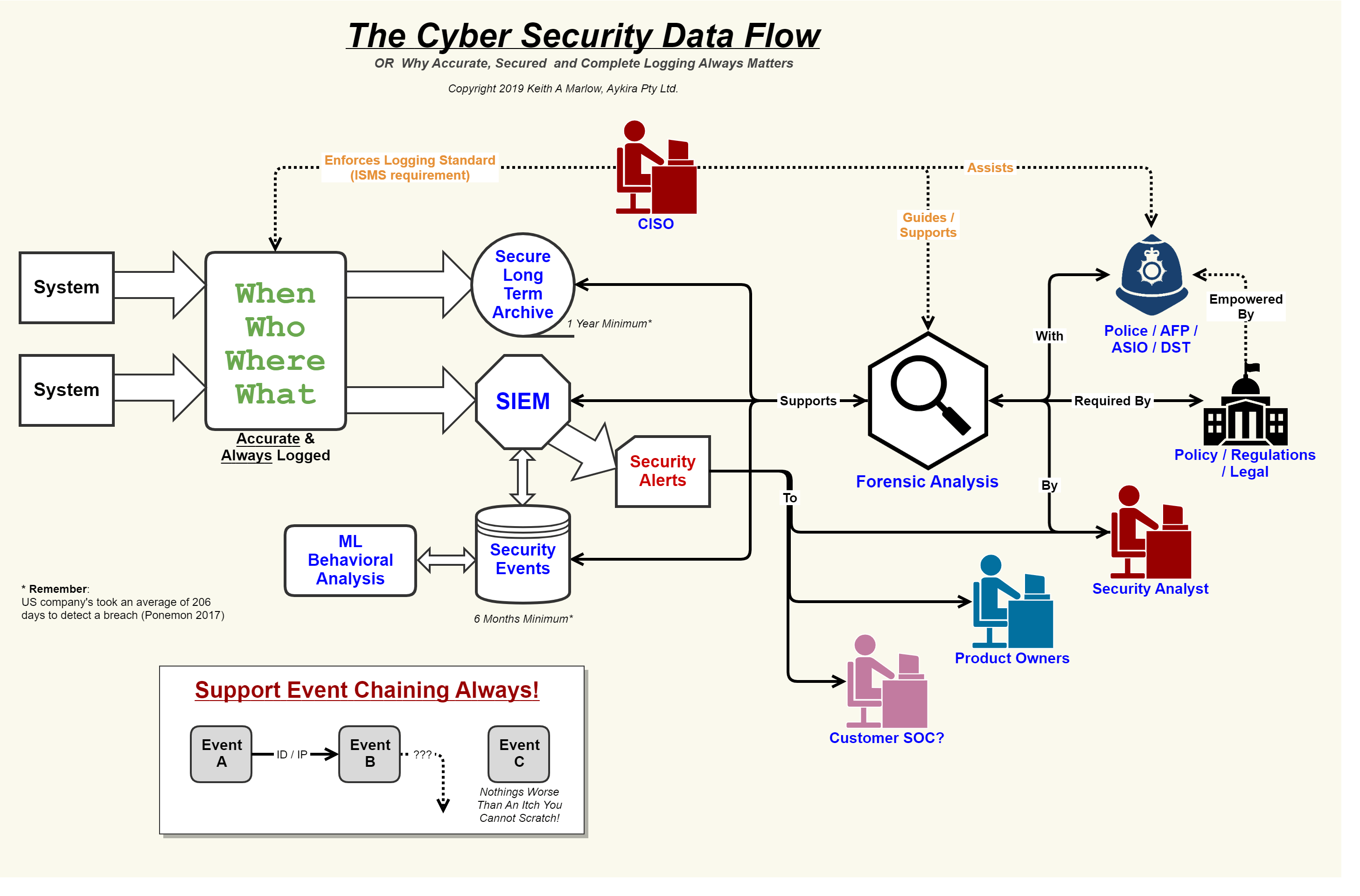
Security Event Logging, why it is so important – Aykira Internet Solutions

Data Flow Diagrams - Mapping Your Way To Better Security - YHB CPAs

Process Flow vs. Data Flow Diagrams for Threat Modeling

Data Flow and Security Overview | Schema App Support